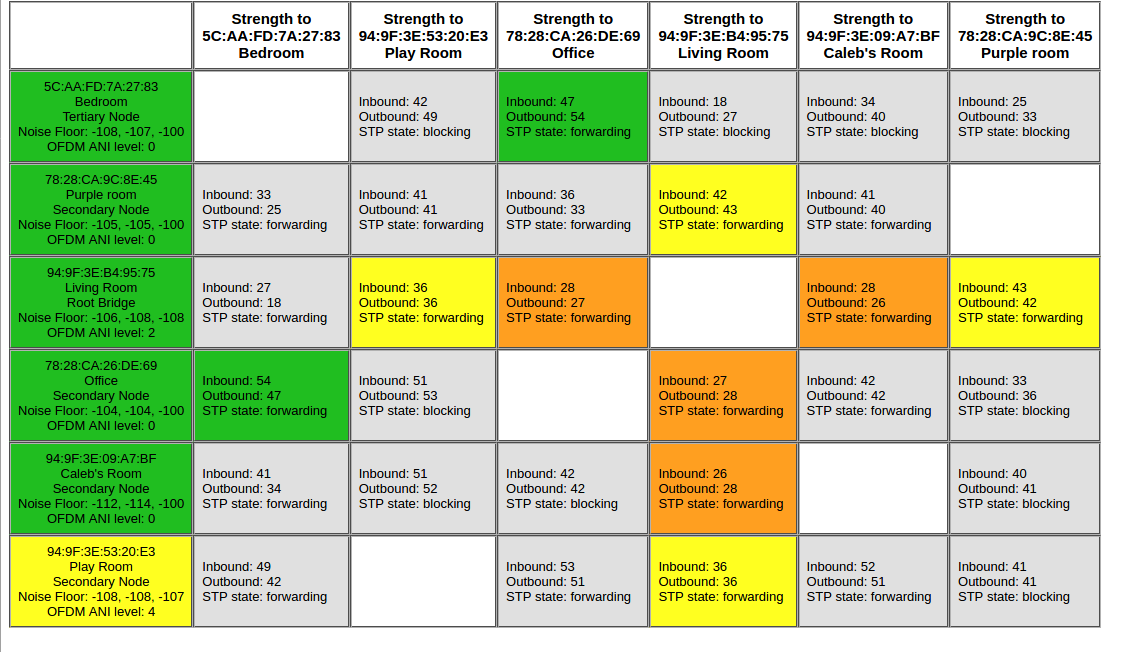
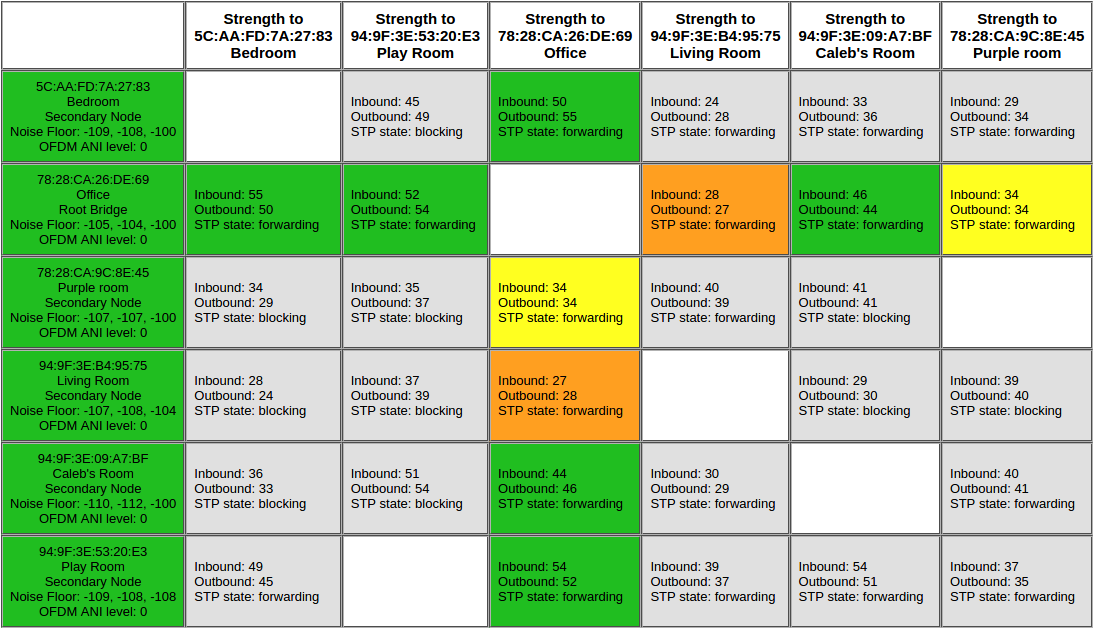
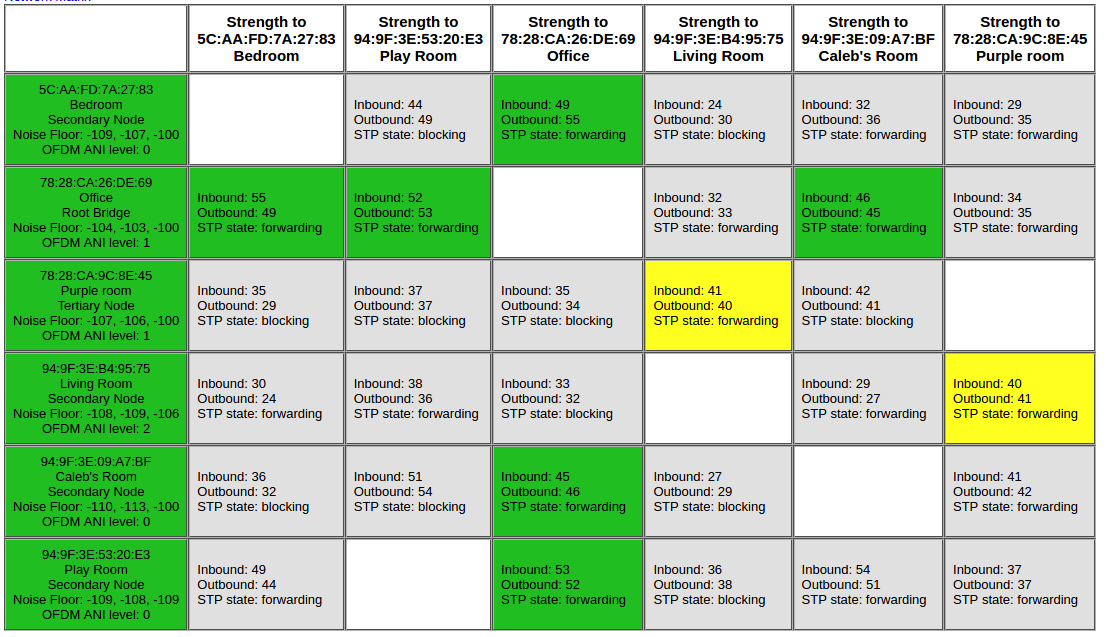
Is it possible to disable the feature of sonosnet that carries non-sonos traffic to an ethernet device connected to a remote speaker? I'll try to explain my setup:
In my office, I have my primary router/internet gateway, various computer equipment, and a sonos Play 1, all connected via ethernet. I also have an ethernet cable that runs from the office to the living room, which is on the opposite side of the house.
I have several other sonos speakers around the house, connected to the other speakers using SonosNet.
In the living room, I have an ethernet switch (connected to the cable from the office) that connects to several devices, including a Sonos Connect, and a second wifi router running in 5GHz-only access point mode.
I was experiencing significant latency/poor connectivity on my laptop when connected to the living room access point, and I couldn't figure out why until my wife unplugged the sonos speaker in the office (thinking it wasn't important), which disabled the Sonos in the entire house, and also disconnected the living room AP and other equipment connected to it from the network. The wired connection between the office and living room was still connected, but it seems it wasn't being used in favor of routing traffic over SonosNet (which went down when the office speaker was unplugged).
The obvious solution is to disconnect the Sonos Connect from the ethernet network, relying only on the speaker in the office to connect SonosNet to the rest of the network. The complicating factor is that I'm doing various small electrical work around the house, and frequently shut off power to various rooms. The router is on a UPS and unaffected, but I'd like the Sonos speakers around the house to keep working when _either_ the speaker in the living room or the speaker in the office have power.
Is there anything I can configure in SonosNet to tell it that there are two nodes with upstream network connectivity, so that it will failover from one to the other? If I put some sort of "smarter" networking device in the living room, like a managed switch or a router, can I accomplish the same thing that way?
I'm a software engineer by trade, and a linux buff, so solutions like editing config files or manually making API calls are easy for me.